- Agentic Intelligence, Agentic Security
- Fabric’s Answers
- What is So Special – and Alarming – about Multi-agent Systems?
- Our Approach
- Understanding Agentic Architectures
- Understanding Agentic Vulnerabilities
- Live Attacks on Your MAS
- Attack Graphs and Paths
- Evolving Attacks through Attack Reasoning and Learning
- Stronger in the Future: Vulnerability Mitigation and Remediation
- Conclusion
- Try Fabric
Agentic Intelligence, Agentic Security
The sheer pace of recent progress in agentic systems has been relentless. Agents have not only become more capable in areas such as open-ended action spaces or code generation but their autonomous behaviors are also becoming more and more emergent. As a result, many areas of software development have struggled to keep apace with the ever-increasing complexity and all its ramifications.
The subdomain in which the lag from unprecedented capabilities to codified best practice is the most evident is security. An unavoidable corollary of the agentic revolution is a rapid proliferation of entirely new kinds of vulnerabilities and threat vectors some of which have never been observed before. If the agentic revolution is the Cambrian explosion of machine intelligence, then the intensification and expansion of security concerns may well lead to a parallel digital pandemic unless a sufficient cure is developed – agentic security absolutely needs to co-evolve with agents.
Today, we release Fabric, a forward-looking security platform for agentic security which builds on our agentic security research. Fabric is the first dedicated security platform for multi-agent systems (MAS) and agentic threats surrounding them.
Fabric is designed to elevate the coverage, reactivity, and productivity of security professionals at all levels, covering individual developers, security engineers, SecOps, CISOs, and CROs. Equally, as a living agentic security layer, Fabric’s deep and sensitive agentic threat modeling enhances and protects agents themselves in constantly evolving and volatile multi-agent environments.
Fabric’s Answers
To a designer, builder, operator, maintainer, end user, or risk underwriter of a multi-agent system, agentic security manifests itself as many and varied problems which need to be addressed at some point.
Fabric is the first dedicated security platform for multi-agent systems and agentic threats which offers optimized modules and services to help you address the most critical security questions and act on them immediately:
- what do I actually have in my agentic system? – understanding your complex agentic architectures and what you have actually vibe-coded and built;
- how does data flow through my agents, and which contexts do they actually deal with? – understanding data and context sources, transformations, flows, and reach across your agents;
- how vulnerable is my agentic system? – identifying and contextualising latent agentic vulnerabilities in your system;
- does my agentic system have any novel, unknown vulnerabilities? – spotting vulnerabilities which are unique to your system beyond what standard static vulnerability databases know about;
- show how my agentic system can be exploited? – running live attack simulations on your agentic system to prove where, when, and how it will break;
- what can I do to protect and harden my agentic system? – robustifying your system through chaos engineering, and offering contextualized remediation and mitigation strategies and fixes for your agent system through tailored security advice, recommendations, and detailed reports; and
- how to keep my security model fresh, relevant, and in sync with my evolving agentic system? – running evolutionary attack simulations which learn continuously and co-evolve with your system.
What is So Special – and Alarming – about Multi-agent Systems?
As is evidenced by the rich and mature praxis of software security engineering and threat modeling, the treat surface and behaviour of any software system tends to come with an incredibly long tail of risk. The current wave of increasingly more agentic AI architectures introduces a large pool of entirely new security complications which can be markedly different from those that surround traditional architectures.
In essence, a typical agentic AI system is one which has most of the following properties:
- is autonomous (up to a certain level);
- is able to observe its environment;
- reasons about its own behaviour;
- maintains some form of memory;
- plans its own behaviour;
- achieves its goals;
- acts and executes actions, and
- uses some tools.
At an architectural level, even a simple (semi)autonomous agentic AI system typically contains a “brain” (a central reasoning and execution model), some form of memory, a planner, an action space for tools and interfaces to external systems, and an execution loop (runtime), to name a few.
If the vulnerability profile and attack surface of a single static system is complex, then the complexity of the security profile of a single dynamic, autonomous AI agent is considerably greater solely due to the joint interactivity of the above kinds of architectural areas and processes, let alone the combined complexity of autonomous behaviours over long time horizons.
To make matters worse, the joint complexity and attack surface arising from the interaction of multiple agents in a multi-agent system will be greater and harder still. Multi-agent systems resemble living organisms whose behaviour cannot be reduced to the kinds of static, localized snapshot scans that have dominated the security engineering and threat modeling tradition up till this point in the history of software engineering.
Continuous multi-agent interaction introduces latent vulnerabilities which can be more than the sum of individual agents’ vulnerabilities, and which can evolve continuously. Traditional static one-shot vulnerability scanners, short-horizon red-teaming environments, and static reactive vulnerability databases are simply not enough to profile and secure living and evolving agentic systems.
Accordingly, true agentic security has to be similarly continuous and evolutionary. A one-shot defense strategy is simply too risky for anyone building agentic systems.
Our Approach
Fabric covers the entire security journey that the builders, operators, owners, and risk underwriters of complex agentic systems care about.
Fabric:
- understands the architectural patterns and behaviours of agents;
- reveals and understands latent agentic security surfaces and behaviors that were not observable before;
- uses security chaos engineering to demonstrate how your system will eventually be broken;
- generates fully bespoke and personalized agentic security reviews, policies, and reports that reflect your unique agentic system; and
- recommends defenses and next steps towards a safer version of your agentic system.
Fabric enables you to go from a one-shot defense strategy to an always-on, continuous-shot mode.
Understanding Agentic Architectures
Our analysis decomposes your multi-agent system into atomic building blocks with which its behavior and security posture can be represented precisely.
Consider a typical multi-agent system at a moderate level of complexity built on a recent agent framework such as LangGraph or Pydantic AI. It is likely that the system
- interacts with the user at some point;
- relies on an LLM back-end (e.g. Grok 4.1);
- uses some kind of supervisor agent which controls some other agents (supervisees);
- uses a few tools; and
- persists some generated data somewhere at some point.
These five basic agentic behaviours and architectural interaction patterns are examples of universal building blocks – agentic primitives – which are ubiquitous in multi-agent architectures. Fabric’s agent topology model recognizes the most common agentic primitives at multiple levels of structural and behavioral granularity and abstraction.
Fabric does not simply recognize agentic primitives in isolation in a piecemeal fashion to try to determine the agentic behavior and the resultant security posture of your system. Our analysis captures the logical interaction and connectivity between all key building blocks covering their structure, roles, responsibilities, and behavior.
For example, a given agent in your multi-agent architecture may communicate with three other agents one of which delegates jobs to other agents: Fabric understands and reasons about the specific security implications of agent delegation and guides your architectural decision-making.
Knowing exactly which inter-agent relations are or will be present in your system is key to precise security modeling. Our analysis captures all critical agent call sequences, flows, communication boundaries, dependencies, control-command hierarchies, and other similar interfaces between agents and other parts of your system.
At the core of our agentic analysis is a taxonomy ****of ****universal agentic primitives which are sufficient to describe and represent a wide range of agent design patterns common to most agentic architectures. A classic example is an agent whose functional role and responsibility is to read something from memory. For example, a financial analyst agent might read 10-K/10-Q text data from a vector DB:
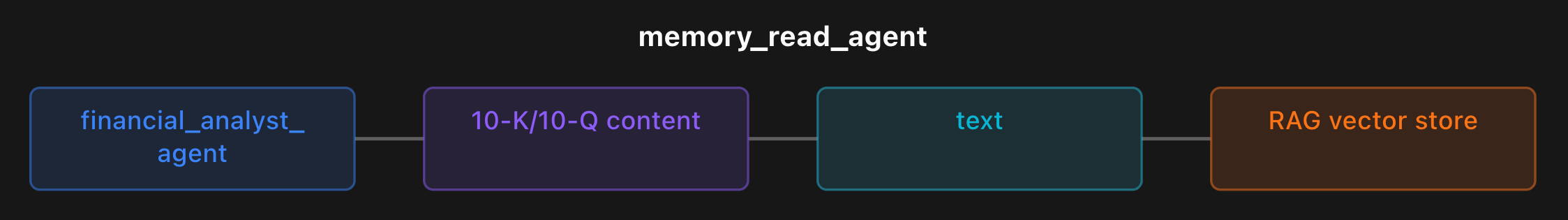
Fabric’s structured core foundation primitives specify exactly which parts of your system are under the scope of the memory-read agent in question. Fabric binds topological primitive instances to exact variables and pointers in your source code, and builds up a coherent, densely connected representation of agents and agent-related components, artifacts, and resources across your agentic architecture.
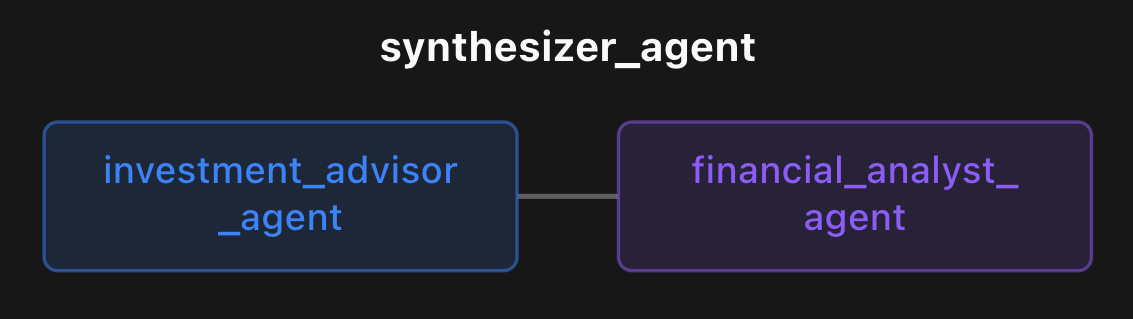
Fabric’s agent topology model also offers extended primitives which capture additional agentic design patterns that might be (more) unique to your specific agentic architecture. For example, Fabric can detect an agent interaction pattern in a financial agent architecture which involves information synthesis between an investment advisor agent and a financial analyst agent:
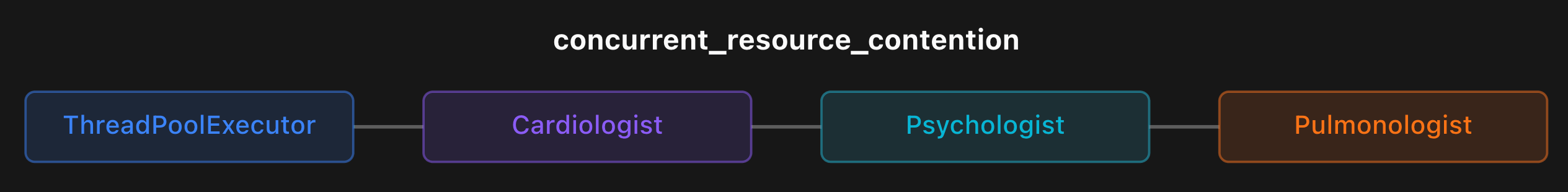
Our topological analysis goes even further in that we identify more abstract higher-order primitives which capture instances of broader agentic behaviors and processes such as HOTL (human-on-the-loop), CoVe (chain-of-verification), and the like whose exact implementation and instances are likely unique to your specific agentic design. For example, Fabric can catch an agentic pattern whereby a shared thread pool is used by multiple agents:
and agentic patterns involving local code execution without sufficient guardrails:
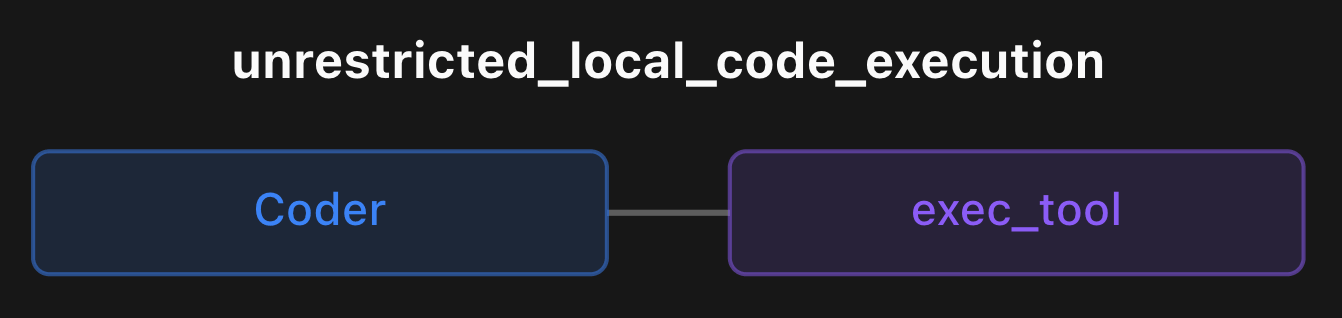
The structured representations used in Fabric’s modeling allow for logical reasoning, deduction, formal verification, and precise control for security professionals.
Understanding Agentic Vulnerabilities
Armed with a thorough analysis of the agentic topology of your system, Fabric projects vulnerabilities onto specific parts of your agentic architecture. For example, if you use an agent to read something from memory, then the specific agent as well as the specific parts, components, artifacts, and resources of your system which interact with the agent (such as a vector store retriever and text persisted in a vector store) can fall under the scope of memory poisoning and related vulnerabilities.
A targeted, structurally and behaviorally conditioned vulnerability model which is able to pinpoint exactly which agents and areas in your system are vulnerable to a specific agentic vulnerability is much more precise and accurate than blind scanning of general vulnerabilities combined with a shallow non-agentic representation of an architecture.
Our agentic vulnerability model covers both known (reported, attested, confirmed) and unknown (not-yet-reported, unattested) vulnerabilities, threats, and exploits.
Traditional vulnerability databases maintained by security practitioners and communities can be precise and effective. Fabric’s agentic vulnerability model includes multiple canonical vulnerability catalogs such as OWASP and more specialized vulnerability databases as well as insights from Moonsong’s agentic security research.
Traditional vulnerability databases are, by definition, reactive and always lagging: a given vulnerability is spotted by someone, then reported, then confirmed, and finally catalogued by security researchers and the wider community. In addition, traditional vulnerability databases tend to be highly localized to specific components or behaviors in static software architectures due to the need for analytical specificity and reproducibility. Owing to the fact that agentic systems are more like living organisms, static post hoc vulnerability databases cannot possibly capture everything in long-horizon tasks that agentic systems ultimately face out in the wild.
Fabric’s extended vulnerability reasoning co-evolves with your agentic system and predicts novel, unknown vulnerabilities emerging from specific contexts, parts, levels, and stages in your unique agentic system.
Tracking novel, unknown vulnerabilities allows you to stay ahead of your attackers.
Live Attacks on Your MAS
Fabric uses the multi-level agentic security intelligence that it has collected about your agents to test the vulnerability, resilience, and stability of your system through simulated attacks which are executed in a live attack simulation enclave.
When it comes to an agentic system which orchestrates multiple agents each of which can be vulnerable to multiple vulnerabilities (either individually or jointly), the resultant attack space can grow very large, especially over time. Although each individual agentic vulnerability is certainly important in its own right, it is the sequential interaction between them that introduces even greater, often more latent agentic security risks. When they interact with different degrees of autonomy amongst agents, traditional one-shot scans and static attack simulations simply run out of steam. If an agentic system is a living organism, then so is the attack space that envelops it.
Attack Graphs and Paths
Fabric uses a form of chaos engineering for agentic security based on an exhaustive attack graph. Fabric models all attack paths throughout your agent topology which attackers can use to break, destabilize, and hack into your system. Fabric’s attack graph captures not only inter-agent connectivity but also paths linking agents and other parts of your agentic architecture.
For example, a possible attack path across a given multi-agent architecture for text generation might
- first exploit a semantic scope evasion (”masquerading”) vulnerability which exploits the decision boundaries of a topic classifier in an agent using a verbose, highly distinct preamble that strongly correlates with some permitted topic which eventually allows out-of-scope and potentially harmful interactions to bypass a scope enforcement agent;
- then fool an evaluation agent which tries to determine the trustworthiness of generated text content via contextually plausible but factually incorrect information; and
- then destabilize a final critic agent by causing a resource-intensive logical deadlock to happen where the critic node rejects fake trustworthy answers which then forces an upstream text generator to try again, and getting rejected by the critic agent again and again, eventually burning massive API credits and computational resources (a form of Denial of Service attack).
This example highlights the sheer range, adversarial creativity, and specificity of potential attack methods that agentic systems will have to endure at runtime.
Fabric’s agentic attack graphs yield attack paths at different depth, coverage, and sensitivity levels ranging from quick “lightning attacks” to exhaustive brute-force distress to match your attack simulation requirements.
Evolving Attacks through Attack Reasoning and Learning
Fabric augments agentic attack paths through in-context attack reasoning, planning, and continual learning to optimize its live attacks dynamically to learn how to attack a specific area of a system, allowing its adversarial capabilities to become more successful and more efficient over time.
Fabric’s continuous attack reasoning evaluates attack path execution potential, effectively designing dynamic attack objectives, goals, multi-turn attack mission plans with attack tactics, intents, and dynamic adaptation triggers. Fabric combines its structural understanding of your specific agentic architecture with generalized skills, traits, task intelligence, and action potential covering standard agent frameworks and their common behaviors and execution patterns.
Fabric generates and executes optimized attack code with recursive self-adaptation loops, retry reasoning, and evaluates behavioral execution evidence of attack success within the attack simulation hyperparameters that you have set. The continual adversarial learning layer of Fabric has access to past attack insights from a continuously growing knowledge base of successful vs. unsuccessful attacks and retry attempts executed previously. Fabric generates novel security intelligence from each attack that it executes.
Fabric co-evolves with your agentic architecture as it learns both how to protect and how to attack your system, allowing you to stay ahead of your attackers.
Stronger in the Future: Vulnerability Mitigation and Remediation
The fusion of Fabric’s rich structural and behavioral model of your agentic architecture combined with in-context vulnerabilities, and the continual adversarial learning layer offers continuous streams of vulnerability intelligence, insights, recommendations, and immediately actionable fixes beyond what any static scanners, red-teaming environments, and vulnerability databases can achieve in traditional one- or few-shot modes.
Fabric provides prioritized defense recommendations from multiple security angles, covering vulnerability severity, highest-leverage mitigation steps, exposed attacks, and bespoke security and safety policies designed for your specific agentic system.
Conclusion
The relentless pace of the agentic revolution has sparked a Cambrian explosion of machine intelligence. As a result, software security struggles to keep up with the rapidly snowballing complexity and the rampant proliferation of agentic vulnerabilities. This can been seen clearly in multi-agent systems (MAS) which are increasingly more vulnerable to entirely new kinds of threat vectors and novel vulnerabilities that traditional static, one-shot security tools simply cannot decipher and contextualize properly.
To address this widening gap, we are releasing Fabric, the first forward-looking security platform dedicated exclusively to agentic threats and multi-agent architectures. Fabric is designed to augment the capabilities of human operators, from individual developers and SecOps engineers to CISOs and risk underwriters, as well as AI agents themselves.
By mapping complex agentic architectures, Fabric guides your agentic security journey from initial problem discovery to final mitigation. Going beyond static scans, Fabric runs live attack simulations and utilizes chaos engineering to actively prove where, when, and how your agentic system will break.
Fabric does not just expose agentic vulnerabilities and risks: it provides contextualized remediation strategies and evolutionary threat models that continuously learn and co-evolve alongside your agentic system.
With Fabric, your security posture remains as dynamic as the agents it protects.
Try Fabric
If you are building or operating AI agents, now is the time to think seriously about security.
Fabric analyzes your agent architecture, identifies vulnerabilities, simulates attack paths, and generates practical mitigation strategies so you can secure your system before attackers find the gaps.
We are opening early access to Fabric and would love feedback from builders working with agents and multi agent systems.
Sign up for early access here.